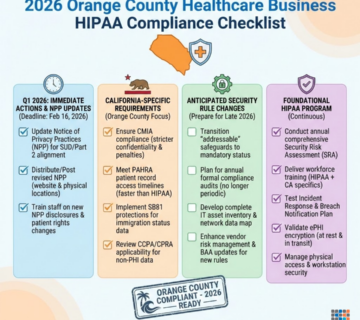
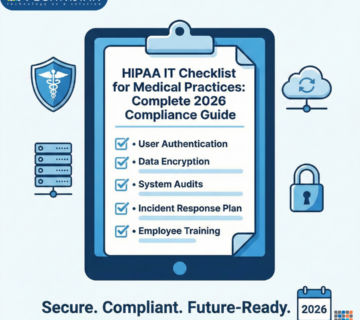
The Real Cost of HIPAA Non-Compliance in California: What Every OC Healthcare Practice Must Know in 2026
HIPAA non-compliance can financially devastate healthcare practices in California. Beyond federal HIPAA fines, Orange County healthcare providers face additional liability from California privacy laws such as CMIA and CCPA, along with costly indirect impacts including legal fees, breach response, patient attrition, cyber insurance increases, and operational disruption. This guide explains the full financial risk of HIPAA violations and outlines how proactive compliance, cybersecurity, and risk management can protect medical practices from devastating regulatory penalties and data breaches. ... Read More